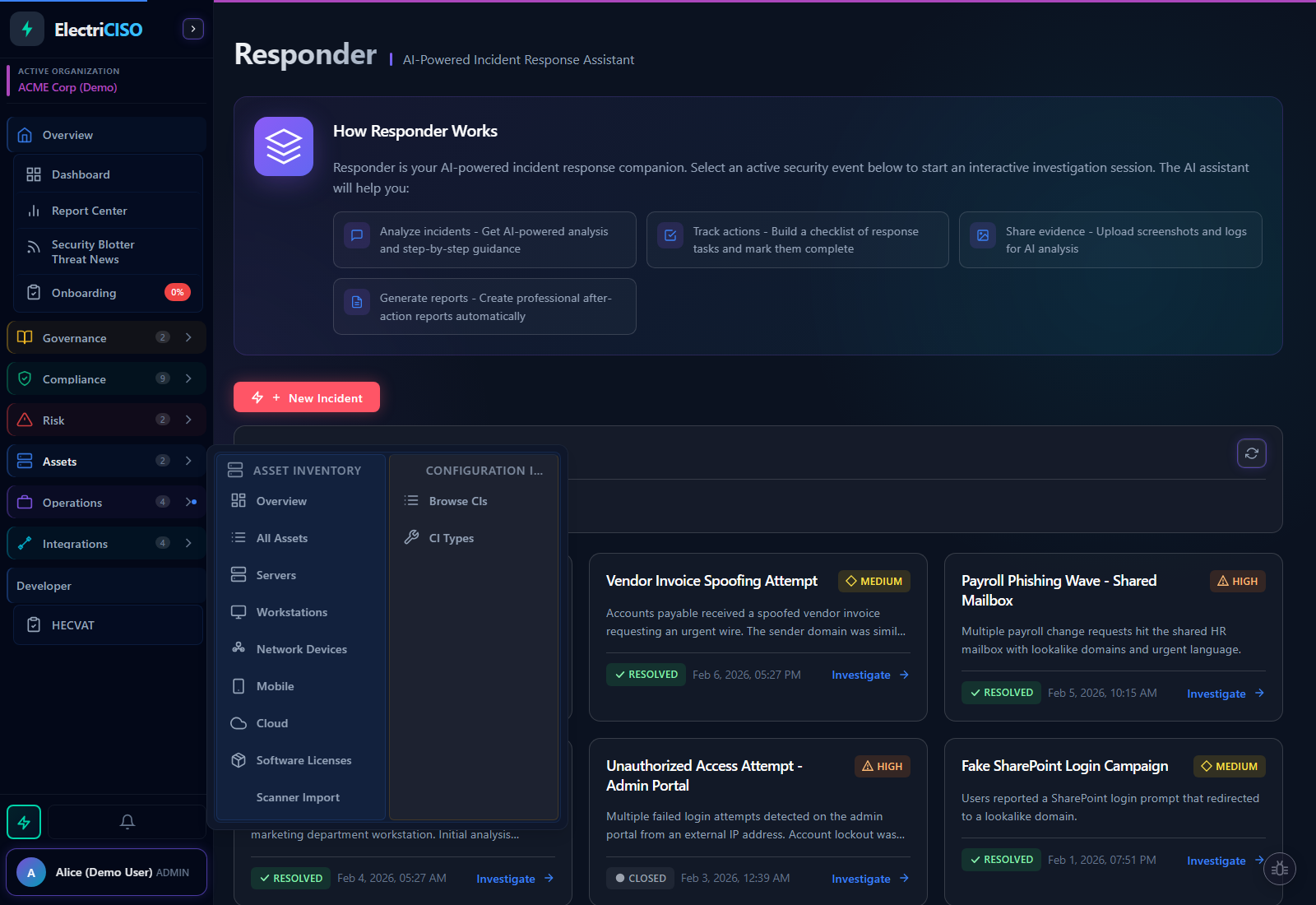
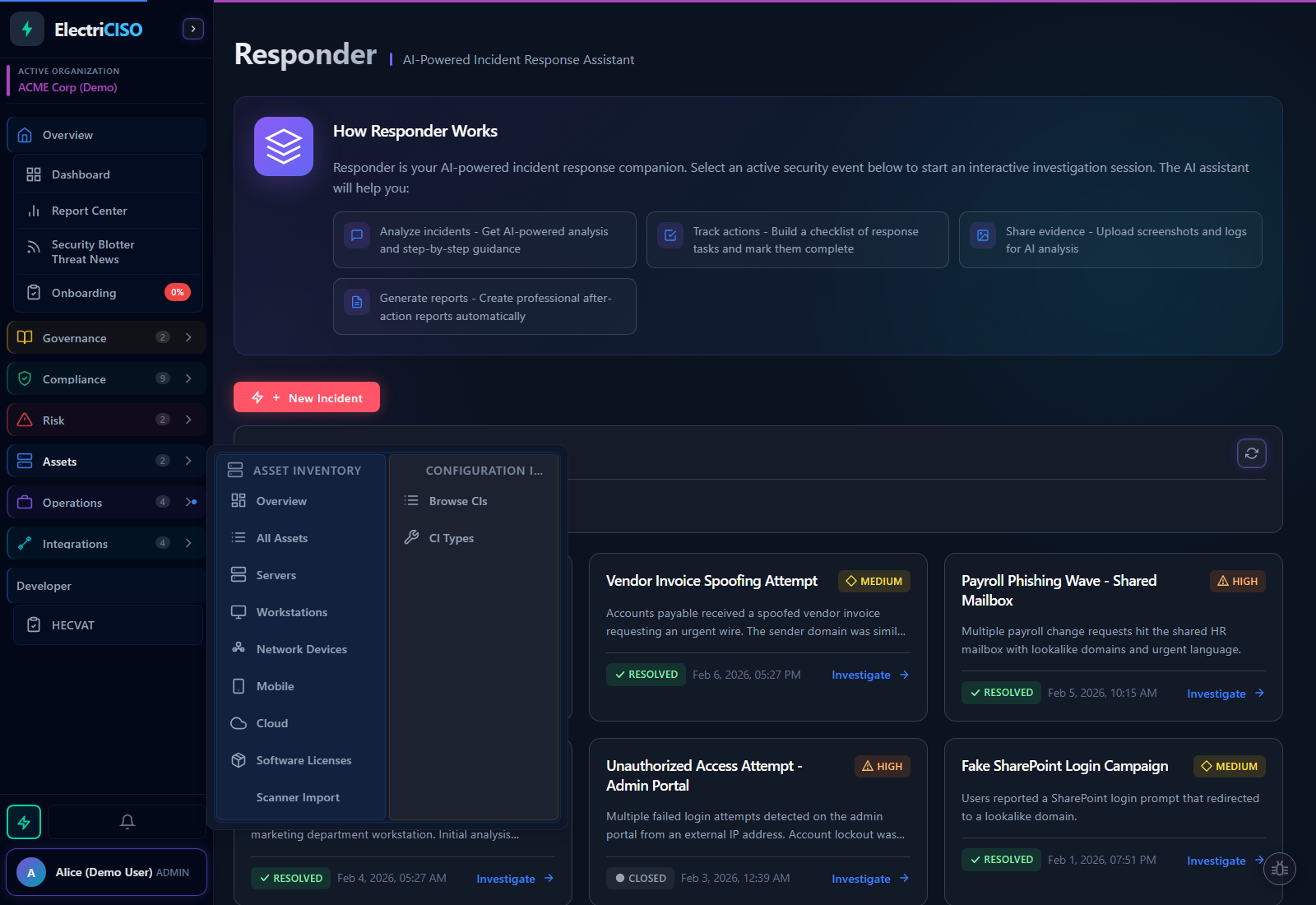
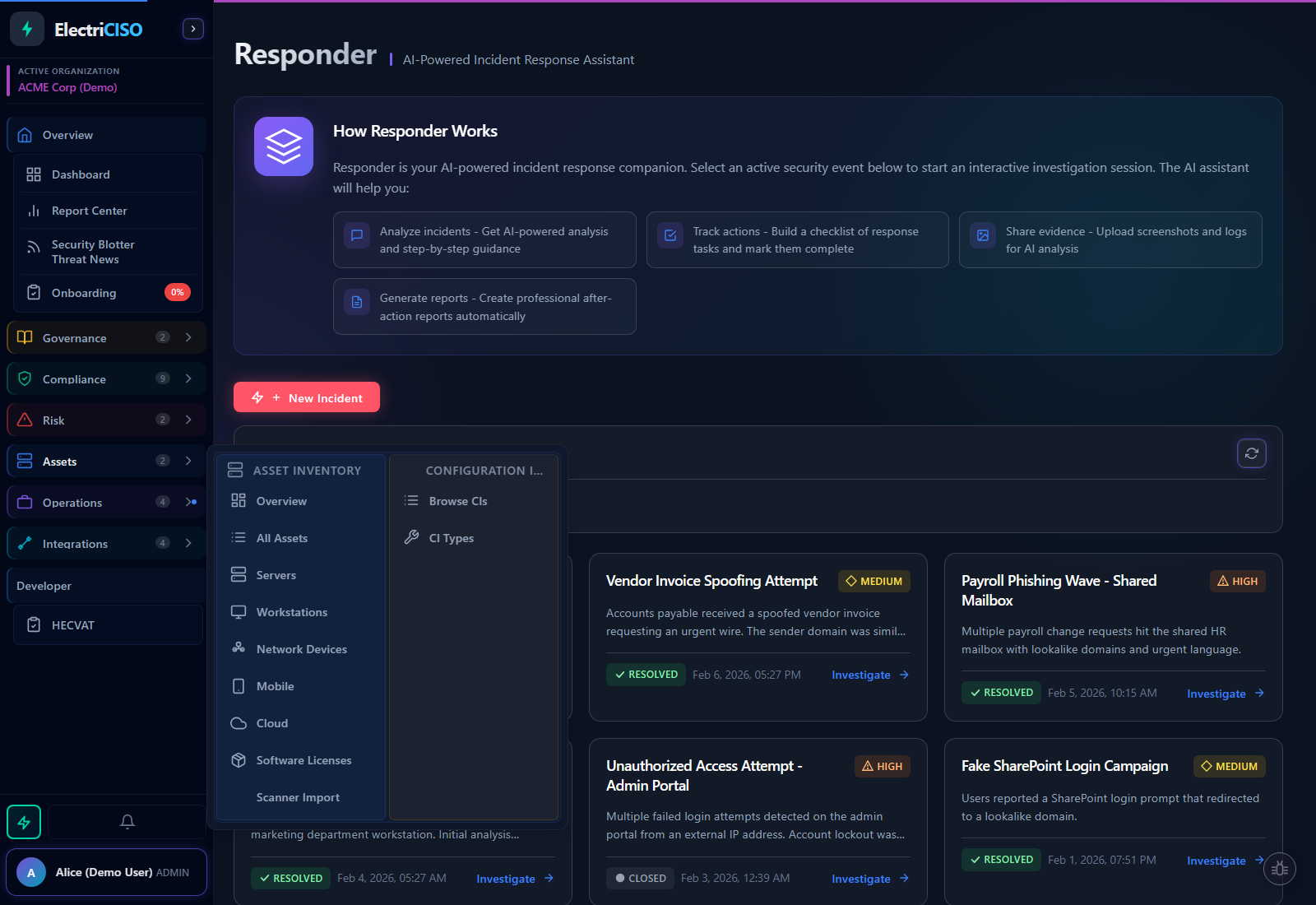
Your AI Co-Pilot
When It Matters Most.
An active security incident is not the time to Google “incident response checklist.” Responder gives you an AI co-pilot that knows your environment, searches live threat intelligence, analyzes your evidence files, drafts your stakeholder communications, and builds your after-action report, while you stay focused on containment.