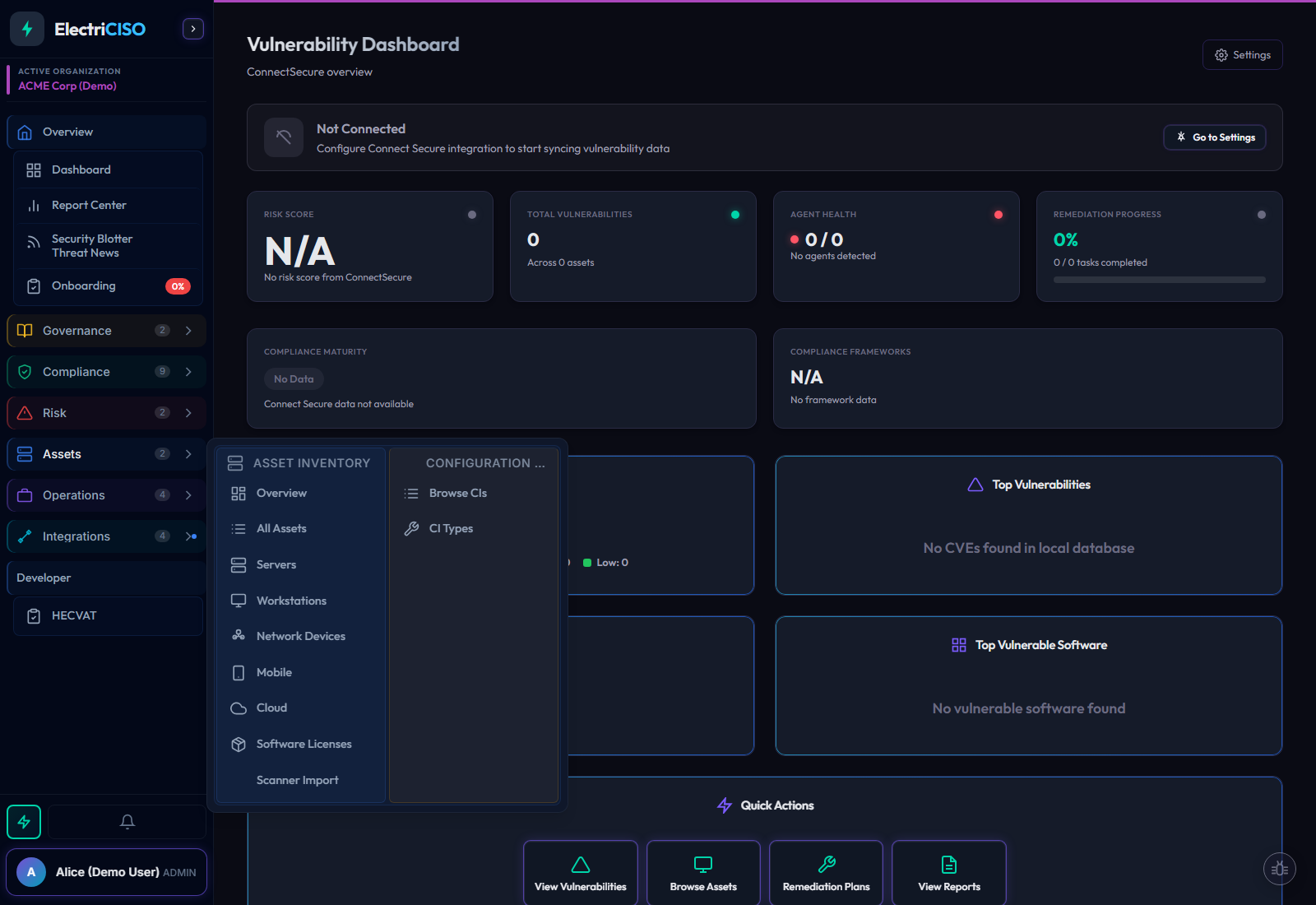
Always current. Seven-phase sync.
A single sync operation handles authentication, asset discovery, vulnerability enrichment, software inventory, compliance checks, CISA KEV cross-referencing, and AI indexing. Run it manually, or schedule it. Your data stays fresh without you thinking about it.
1. Authenticate
OAuth2 token exchange with ConnectSecure V4 API
2. Company Stats
Risk score, compliance maturity, vulnerability summary
3. Asset Merge
Two endpoints merged with deduplication
4. Vulnerabilities
Full CVE detail pull with remediation enrichment
5. Software Inventory
Per-package vulnerability counts and version tracking
6. CISA KEV Enrich
Cross-reference every CVE against the Known Exploited catalog
7. RAG Indexing
SHA-256 differential embedding for AI-powered search
Automatic Scheduling
Manual, hourly, daily, or weekly sync frequency