One Inventory.
Every Asset That Matters.
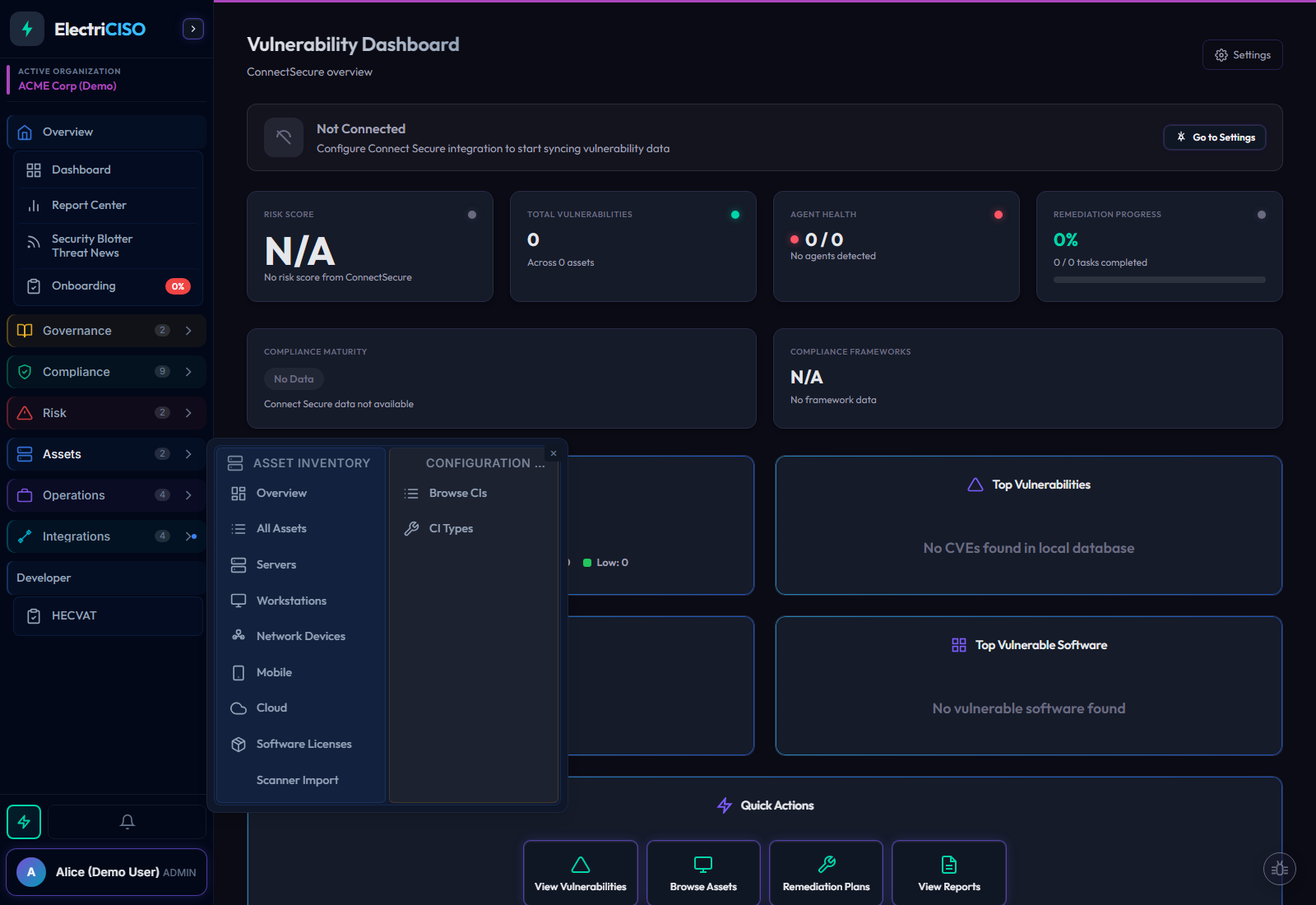
Track 11 asset types from 7 source types, keep configuration items and M365 devices in the same system, and connect every asset to vulnerabilities, risks, vendors, and compliance work. When a finding lands, you already have the operational context.